Product Details
Morphisec’s powerful Moving Target Defense based protection keeps your organization secure against the threats that pose the most danger.
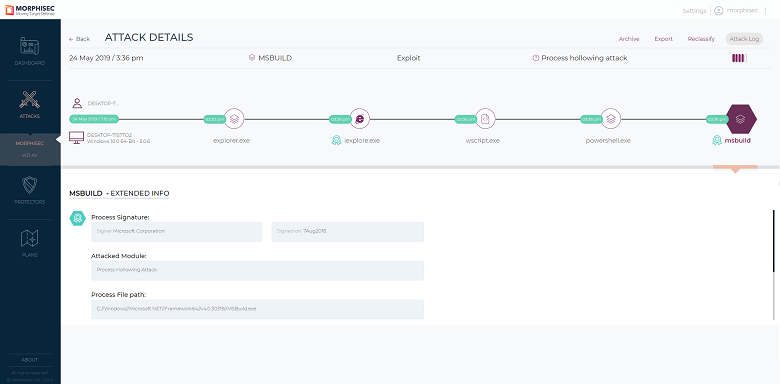
Earliest-Stage Proactive Threat Prevention
It natively prevents all zero-days, advanced memory-based threats, malicious documents and browser-based attacks before they execute, no detection or hunting required. Morphisec reduces prevention time of unknown attacks to zero and does not generate alerts to investigate, analyze or remediate. Security teams cut operational costs while drastically reducing organizational risk.
Simple to Operate
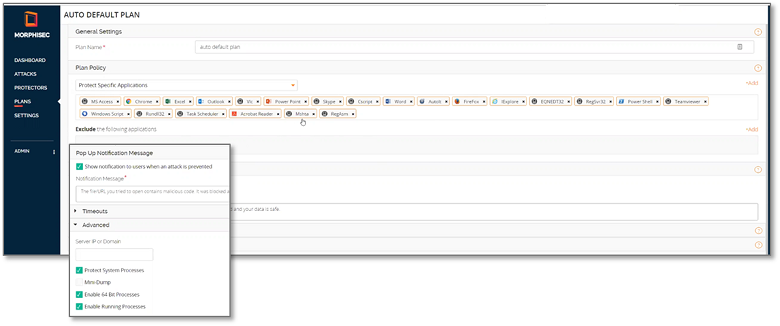
Morphisec Unified Threat Prevention is a single agent solution that installs quickly, requires no management or monitoring, has no runtime components and zero performance impact. An on-premise or cloud-based management console provides complete visibility into organization threats and effortless control over settings and functionality. Moving Target Defense virtually patches vulnerabilities in your applications and operating systems so IT teams can patch to their schedule. It functions seamlessly across virtual, physical or hybrid IT environments, no internet connection required.
PREVENT ADVANCED UNKNOWN THREATS INSTANTANEOUSLY: Natively prevents zero-days, fileless memory attacks, malicious documents and browser-based threats at the moment of attack
SET AND FORGET: Quick and easy deployment, virtually zero management, no need to investigate or analyze, no false positives and no system conflicts
ALL VDI ENVIRONMENTS: Functions seamlessly across virtual, physical or hybrid IT environments, whether on-premise or in the cloud.
PRESERVES YOUR VDI INVESTMENT: Does not lower VM consolidation ratios; no increase in cost and complexity
VIRTUALLY PATCHES VULNERABILITIES: Keeps your VDI protected from exploitation of unpatched vulnerabilities in applications and operating systems.
EXTREMELY LIGHTWEIGHT: Invisible to end-user with light 2Mb footprint, no performance penalty and no updates or scans.
Screenshots

Resources